Data Security and Privacy Statement
Pactiv Evergreen recognizes the importance of an effective security program to protect the company’s employees, assets, products, data, systems, property, and reputation from potential threats. This security disclosure provides information about how Pactiv Evergreen demonstrates engagement and commitment to building stakeholder confidence and trust as the cybersecurity risk landscape evolves.
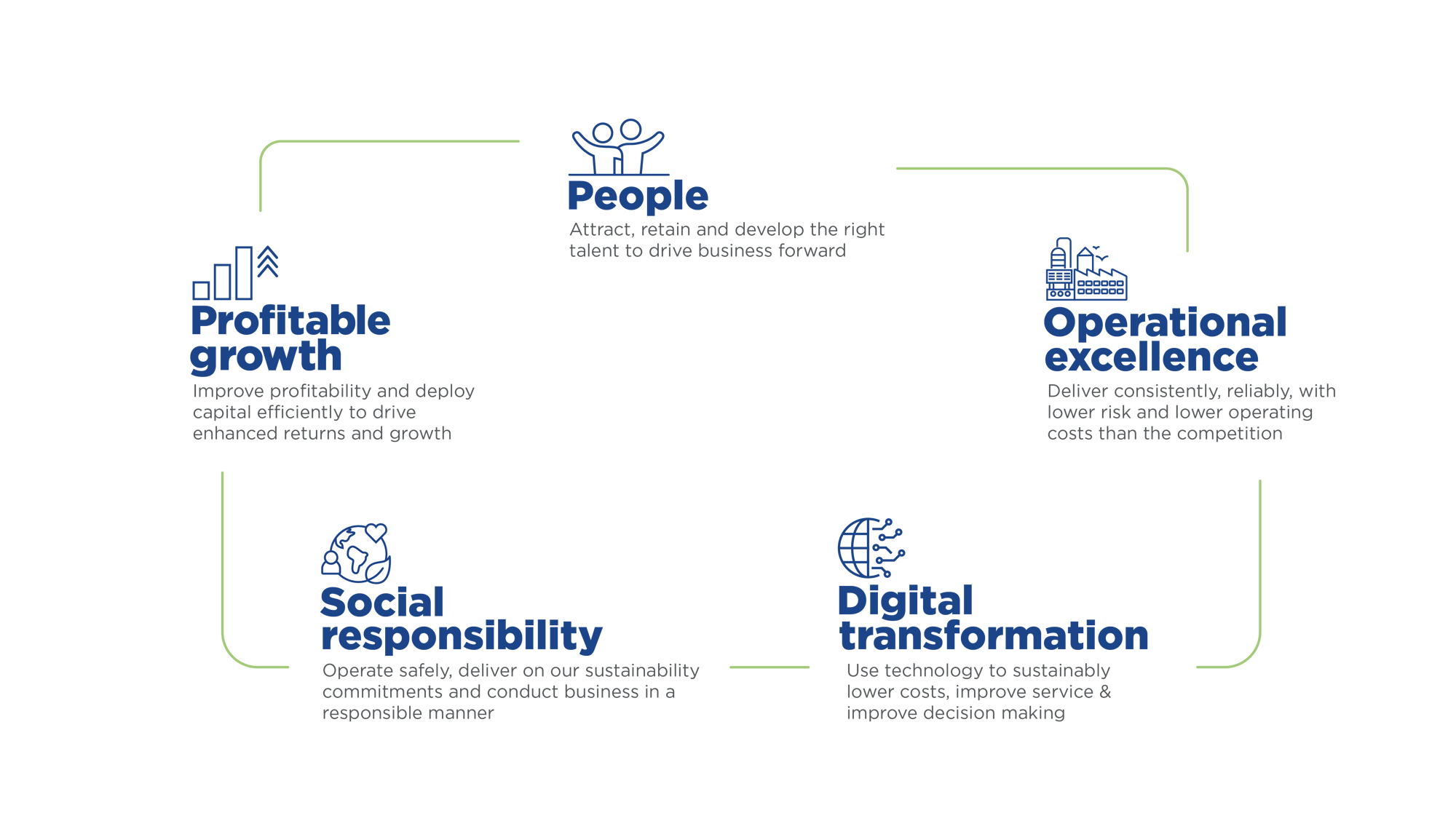
Pactiv Evergreen’s commitment to security is guided by Five Strategic Principles: People, Operational Excellence, Digital Transformation, Social Responsibility and Profitable Growth.
People
Policies
Pactiv Evergreen has developed, implements, and maintains written information policies, processes, and controls to detect, respond to, mitigate, and recover from cybersecurity events that are not prevented. These technology and security policies and procedures set forth certain administrative, technical, and physical safeguards that are designed to protect the company’s information technology assets and data, and by which all employees are expected to abide.
Training
Pactiv Evergreen provides numerous training programs designed to mitigate risk by helping users understand the role they play to combat information security breaches and strengthen user knowledge on information security-related issues. Awareness trainings such as the monthly Cybersecurity newsletter publication, periodic simulations, and required training help users understand risks and identify potential attacks they may encounter as they receive email and use the internet.
Whistleblower Procedures
Pactiv Evergreen has a published Whistleblower policy for reporting concerns related to accounting, auditing, ethical violations or other concerns without fear of dismissal or retaliation of any kind. Included are established procedures for the receipt and handling of complaints, including those submitted by employees and other interested parties. Employees with concerns may report their concerns to their direct supervisor or the Chief Legal Officer, or on a confidential or anonymous basis to the Chief Legal Officer or to a hotline.
Security Roles and Responsibilities
A Cybersecurity Steering Committee exists to provide executive engagement, oversight and responsibility with respect to protecting Pactiv Evergreen’s information assets and operations. The focus of the Steering Committee is to assist Pactiv Evergreen’s Board in overseeing the protection of Pactiv Evergreen’s information assets and operations. The Steering Committee ensures the alignment of the information security strategies with the business objectives.
A Cybersecurity Working Group exists to support the implementation and rollout of cybersecurity programs and projects. The Working Group maintains the currency and compliance of policies and champions cyber awareness across the enterprise.
The Cybersecurity Team is staffed with appropriately skilled individuals across disciplines – Security Operations, Compliance and Architecture - and works in close collaboration with the business and IT departments.
Operational Excellence
Control Environment
Pactiv Evergreen’s internal control environment is self-assessed by control owners and formally audited by internal and external audit on a no-less-than-annual basis in accordance with requirements established and monitored by the Audit Committee of Pactiv Evergreen’s Board. A Risk and Control Matrix for Information Technology General Controls is maintained.
External Audits
External audits include evaluations of the design and effectiveness of information technology-related controls (access, changes and operations) of applications with impacts to financial reporting. These audits also include evaluations of Sarbanes-Oxley, or SOX, controls related to third parties as well as an evaluation of third-party Service Organization Control 1 (SOC1) reports.
System Development Life Cycle
Protocols and standards exist for the development and life cycle management of systems and applications as well as standardized protocols and methods for appropriate, efficient, and prompt handling of all IT change requests. These standards and protocols are in place to ensure that the IT team implements changes to the production environment in a manner that ensures appropriate control measures are in place, that all necessary parties are notified in advance of the changes, and that implementation schedules are coordinated with other activities and teams.
Data Protection
Pactiv Evergreen employs a multi-layered approach to protecting data from unauthorized access or disclosure, including, but not limited to:
- Internal controls are in place for employee and third parties to restrict physical or digital access to Pactiv Evergreen systems, data and locations. Requested access is evaluated and approved by management and follows the principle of least privilege to ensure that only those accesses which are essential to perform the intended functions are provisioned.
- Consistent use of multi-factor authentication.
- Pactiv Evergreen’s network and emails are scanned 24/7 for threats. The Security Operations Center conducts appropriate and periodic vulnerability scans.
- Evaluation of vendor responses to a technology questionnaire covering Authentication & Application Security and Infrastructure and Data Review, including physical and digital access to data.
- In accordance with established SOX IT internal controls, periodic user access reviews are performed on financially relevant applications and third party access must be approved on a semi-annual basis.
- Service Organization Control 1 (SOC1) reports are required of third party applications with financial relevance, which include testing of physical and digital access to data.
Incident Response
A Cybersecurity Incident Response Plan exists and contains procedures that cover identifying, investigating and responding to potential cybersecurity incidents in a way that minimizes impact to Pactiv Evergreen.
The Cybersecurity Incident Response Team of authorized personnel receive reports of possible Cybersecurity Incidents. The team handles any immediately necessary action related to containment and protection of the Pactiv Evergreen IT environment, conducts investigation and analyses, and provides reports to Pactiv Evergreen management with a recommended follow up responses.
Assessment of Third Parties
Pactiv Evergreen employs a multi-layered approach to review and assessment of third parties, including, but not limited to:
- Evaluation of vendor responses to a technology questionnaire covering Authentication & Application Security and Infrastructure and Data Review, including the technology categories of certifications, identity, domain verification, testing lifecycle, logging, hosting, personally identifiable information (PII), and encryption as applicable to the situation.
- IT Procurement evaluation of the vendor to meet IT standardization practices for Pactiv Evergreen.
- Signed/countersigned Master/Professional Services Agreements (MSA/PSA), Statements of Work (SOW), and Non-Disclosure Agreements (NDA). The contractual requirements ensure that transactions are executed as intended and under applicable law, regulations, and company policy.
- Annual internal and external audits on the design and effectiveness of information technology-related SOX controls (access, changes and operations) of third parties providing software-as-a-service (SaaS) applications with impacts to financial reporting.
Digital Transformation
Operating Model and Roadmap
Pactiv Evergreen has aligned our operating model to our business strategy in order to deliver priority activities efficiently and effectively. Expert outcomes- and knowledge-based services are activated through digital and analytical platforms supported by a combination of Shared Services and Centers of Excellence models.
An enterprise, digital and analytics strategy roadmap was developed to support and address project delivery and adoption of digital solutions. Updated digital collaboration models within the business units were implemented to accelerate solution and value delivery processes. A realignment of roles was performed to ensure capabilities exist in the right places to drive creation and adoption of digital transformation.
Risk Assessment
Information security risk assessments are performed regularly by Compliance, Internal Audit and External Audit that identify and analyze likelihood and significance of potential events that may impact individuals, assets and/or the security environment. The assessments help management to prioritize specific activities and/or expenditures.
Social Responsibility
Data Privacy
Pactiv Evergreen is committed to protecting and treating responsibly the data entrusted to us of our customers, vendors, employees and website visitors. We do this through adherence to policies of data classification that protect sensitive information and support compliance with applicable privacy laws, ongoing data mapping, and execution of Information Technology General Controls.
Profitable Growth
Business Resiliency - BCP & DR
Pactiv Evergreen maintains Business Continuity Plans (BCP) designed to ensure critical services and products continue to be delivered during a disruption. The accountability for ensuring that a robust BCP is in place rests with the business/site manager, with appropriate IT support. Included are:
Plans, measures and arrangements designed to ensure the immediate, continuous delivery of critical services and products, and to permit the organization to continue to operate while recovering its facility, data and assets.
Identification of necessary resources to support on-going business continuity, including personnel, information, equipment, financial allocations, legal counsel, infrastructure protection and accommodations pending full recovery of normal operations.
Records Retention
Pactiv Evergreen has a Records Retention Schedule designed to identify and describe, in one document, all types of records pertaining to the operations and functions of Pactiv Evergreen, as well as the retention schedule in months and years for each record type. This record retention schedule demonstrates compliance with statutory and regulatory recordkeeping requirements for administrative, financial, legal and historical records as well as helps to reduce litigation risks.
Disclosures
Pactiv Evergreen complies with all applicable disclosure requirements, including those under the securities laws to disclose information about material risks, as well as other disclosure requirements, including under applicable breach notification laws relating to security risks and events.